Fortune 500 companies with incident response teams and plans in place are pessimistic about their effectiveness amid a climate of data breach domination.
September 24, 2014
Just because you have an incident response plan and an incident response team doesn't mean your organization is ready for a data breach.
Nearly three-fourths of US Fortune 500 companies now have set up incident response plans and teams in preparation for cyberattacks, but only one-third of them consider their IR operations actually effective in the face of a data breach, according to a new study.
The good news is that companies are creating IR plans and teams more than ever: 73% of Fortune 500 firms this year have IR plans versus 61% last year, and 72% this year have formed IR teams versus 67% last year, according to a new report by the Ponemon Institute. The bad news is that most of their C-level and above executives don't feel ready to handle a data breach and its fallout: 68% say their company would not be able to handle negative publicity in the wake of a breach, and 67% say their organization does not know the steps to take after a breach to ensure loss of their customers' and business partners' confidence and trust.
"They are more prepared, but not practiced, in data breach response," says Michael Bruemmer, vice president of data breach resolution at Experian, which commissioned the report on data breach preparedness. "Despite increased awareness, the business leaders who responded [to the survey] are not necessarily confident in their company's response."
Why the long faces? It could well be the constant wave of high-profile breaches -- mainly major retailers -- that has dominated the news this year, or maybe organizations have finally reached the acceptance phase of the inevitability of being breached. "Honestly, I think the Target breach was a watershed moment for those people saying 'it won't happen to us.' It happened at a very bad time for Target--right before Christmas and the holiday shopping season," Bruemmer says.
Target had a large security team, state-of-the-art security tools, but still got burnt. "Data breach preparedness is a team sport, not a compliance exercise," he says. "Just having a plan in place is not enough... It's about rebuilding brand reputation... That is part of the concern reflected in the results of this study.
So why are aren't Target, TJ Maxx, and others sharing their war stories to help the next potential victim?
Radio silence is the common aftermath of a big data breach. "Nobody has been talking about how to handle a breach. I hate to say it but Target, Home Depot, and other companies have been [noticeably silent there]. I haven't seen a lot of 'here's how we handled it, best practices and what we've learned," says Sean Mason, global incident response leader at CSC.
The lack of postmortem discussion is likely due to corporate legal teams urging silence rather than full disclosure. "I don't know if it's a liability thing" for these companies, Mason says. "But the large CERTS and SOCs that are more established and who know their stuff inside out and have gone through battle after battle speak out at conferences," he says.
Lockheed Martin, for instance, went public with how its renowned "kill chain" security architecture helped it detect and shut down an intruder in its network using legitimate credentials, including a stolen SecureID token in the wake of the RSA breach. The attacker used valid credentials of one of Lockheed Martin's business partners, and got caught red-handed when the defense contractor's security tools detected uncharacteristic data access by that user.
[A rare inside look at how the defense contractor repelled an attack using its homegrown 'Cyber Kill Chain' framework. Read How Lockheed Martin's 'Kill Chain' Stopped SecurID Attack.]
Peter Clay, CISO at CSG Invotas, says given that companies that were fully compliant with their industry standards (think PCI) and regulations still get hit, the market is moving toward data protection rather than pure compliance driving enterprise security strategies. "The impact on their business was signficant," Clay says of the retailers that have been hit in the past year. "There are executives losing their jobs."
Having an IR plan in place isn't enough, either. Organizations need to practice deploying incident response plans with regular simulations, akin to fire drills.
"So it's great you have a plan. But a plan is just guidelines... a template. That's not the answer, especially if you don't have people practicing it day in and day out," CSC's Mason says. "We've seen a lot of customers not necessarily asking for help in the IR plan, but on tabletop exercises" for it, he says.
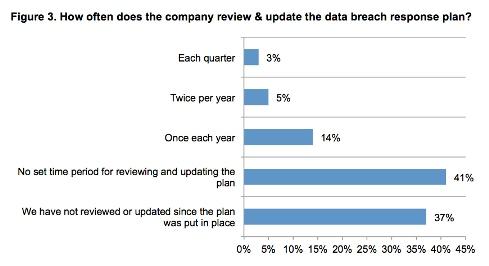
To top it off, there's very little review and updating to existing IR plans: nearly 40% say they haven't reviewed theirs since they created it, 41% have no set timeframe for reviewing it, and 14% say they review theirs yearly, according to Ponemon's report.
Of the more than 560 respondent firms, 43% said they had experienced at least one breach in the past 12 months, up from 10% from the same survey conducted by Ponemon in 2013.
The full Ponemon report, "Is Your Company Ready for a Big Data Breach? The Second Annual Study on Data Breach Preparedness," is available here for download. Meanwhile, data security will be a front-and-center topic next week at Interop in New York City.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024


